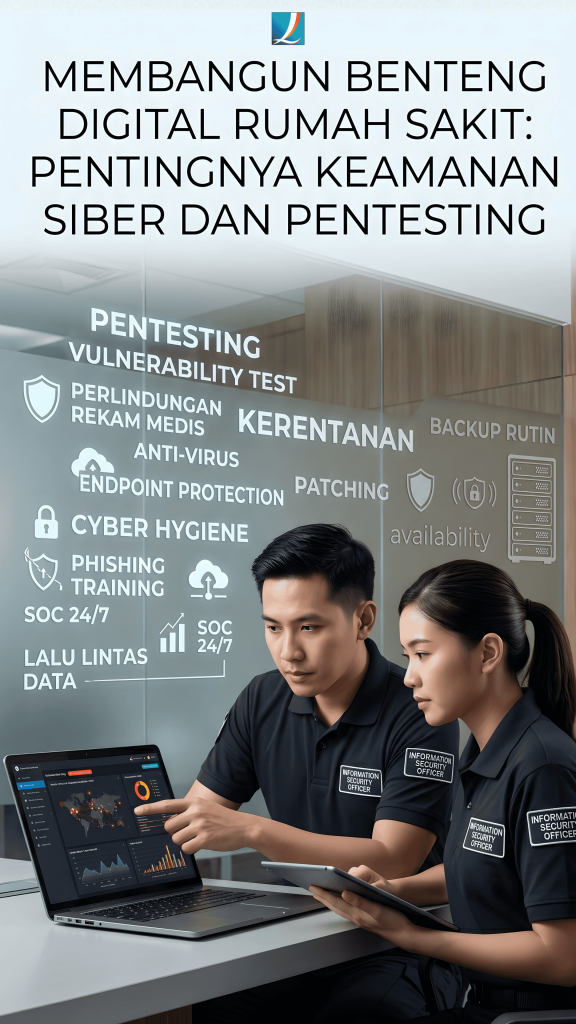
Building a Hospital’s Digital Fortress: The Urgency of Cybersecurity and the Role of Pentesting
In the era of healthcare digitalization, hospital operations are deeply dependent on their technological infrastructure. This digital transformation opens vulnerabilities to massive cyber threats, with Ransomware being one of the most prominent. Ransomware is a type of malicious software (malware) that encrypts a victim’s data and demands a ransom payment for decryption. For healthcare facilities, protecting medical records is not just a technical operational issue; it directly impacts patient lives.
Therefore, let’s dissect crucial cybersecurity strategies from a technical perspective, specifically regarding Vulnerability Testing or Pentesting.
- Understanding Vulnerability Test: Pentesting
In the world of software engineering and cybersecurity, Penetration Testing (Pentest) is a periodic simulated cyberattack process to test the resilience of a system’s architecture against real-world attacks. This practice is conducted legally and ethically by security engineers to find security flaws (bugs or configuration vulnerabilities) in applications and networks before hackers can exploit them. By proactively identifying these vulnerabilities, IT teams can immediately release security updates or patching. - Why Perform Pentesting?
Hospitals are high-value targets for cyber syndicates. Based on the latest reports from the National Cyber and Crypto Agency (BSSN) in 2025, Indonesia experienced a 60% increase in cyberattacks during the first semester, with Ransomware remaining a frequent and destructive threat to vital infrastructure.
The impact of cyberattacks on health infrastructure can be fatal:- German Incident: A ransomware attack at Duesseldorf University Clinic paralyzed the hospital system and forced the closure of the emergency department. This required a patient with a life-threatening condition to be diverted to another hospital 32 km away, leading to delayed treatment and the patient’s death.
- UK Incident: At the NHS London network, disruptions to pathology services due to ransomware caused delays in blood test results, which were confirmed to contribute to a patient’s death.
Periodic pentesting is an absolute procedure to ensure every vulnerability in the health network is closed, protecting the availability of hospital systems and patient medical records. - Prevention and Mitigation Strategies
In addition to system testing through pentests, a layered security architecture is required:- Routine Data Backup: Perform data backups regularly, both offline and using trusted cloud services, so data can be restored at any time.
- Endpoint Protection: Use official anti-virus and endpoint protection software, and ensure all software and operating systems are updated automatically.
- Cyber Hygiene: Train all medical and administrative staff to be aware of phishing threats and practice good cyber hygiene.
- Security Operations Center (SOC): Establish a SOC for 24/7 network monitoring to detect, analyze, and respond to data traffic incidents quickly.
Important: If a data hijacking incident occurs, avoid paying the ransom as it motivates criminals to continue. There is no guarantee that hackers will provide the decryption key, and the risk of re-infection or permanent file damage remains high.
Medinfras Commitment to Hospitals
As the developer of the Hospital Management Information System (SIM-RS) Medinfras, PT Quantum Infra Solusindo realizes that hospital database security is non-negotiable. We prioritize cybersecurity as our primary code foundation.
We ensure to all our customers that Medinfras has implemented strict and continuous software and infrastructure pentest procedures. This preventive step ensures that the software ecosystem supporting your operations is free from dangerous injection or exploitation gaps. Through a strong mitigation commitment, we guarantee that all customer data and patient medical record privacy will always be protected from all forms of cyberattacks.